In this digital age, email has become an indispensable part of our lives. It’s convenient, fast, and helps us stay connected. However, this convenience has created a breeding ground for fake emails and scammers looking to deceive unsuspecting individuals.
One prevalent tactic used by these fraudsters involves them posing as legitimate companies to try and trick people into divulging sensitive information, or falling for their scams. In this article, we will break down how scammers operate and provide tips on how to protect yourself from falling victim to fake emails.
Understanding the Scammer’s Approach
Scammers are masters of deception, and they have perfected the art of imitating reputable companies. They study the real emails sent by genuine businesses, learning their language, format, and design. Then they create fraudulent emails that look incredibly authentic. These emails often include logos, branding elements, and even the names of real employees to show credibility.
Red Flags to Look Out For

TOZO T10 Wireless Bluetooth Earbuds
The Tech Boomer recommends these wireless bluetooth earbuds. Clear, crisp sound—plus they’re easy on the wallet!
View on Amazon →This post may contain affiliate links. As an Amazon Associate, I earn from qualifying purchases.
While scammers can be crafty, there are certain red flags that can help you spot a fake email:
Urgent Requests
Scammers often create a sense of urgency, urging you to act quickly. They may claim your account is compromised or that you won a prize that expires soon. This is a sure sign of a fake email. Legitimate companies rarely pressure customers like this.
Suspicious Links
Be wary of any links in emails, especially those that redirect you to unfamiliar websites. Hover your cursor over the link without clicking to see the actual URL, or, if you’re on mobile, long press on the link to show it. Legitimate companies typically use their own domain names such as “homedepot.com,” “bathandbodyworks.com,” etc.
Unprofessional Grammar and Spelling
Genuine emails from reputable companies are well-written and error free. Since many of these scammers come from other countries (Kolkata, India is a hot bed of scammers), they often make grammar and spelling mistakes that can give them away.
Request for Sensitive Information
Legitimate companies would never ask for personal information, such as passwords or social security numbers via email. If an email requests such data, it’s likely a scam.
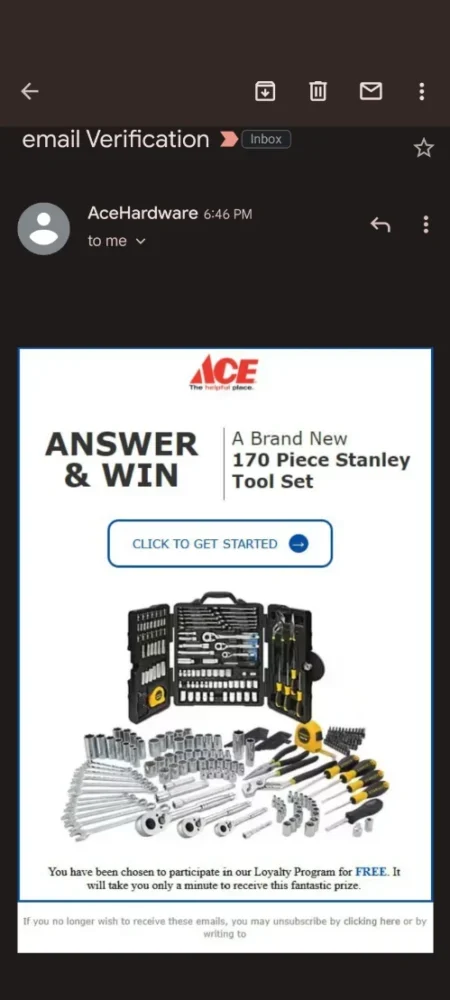
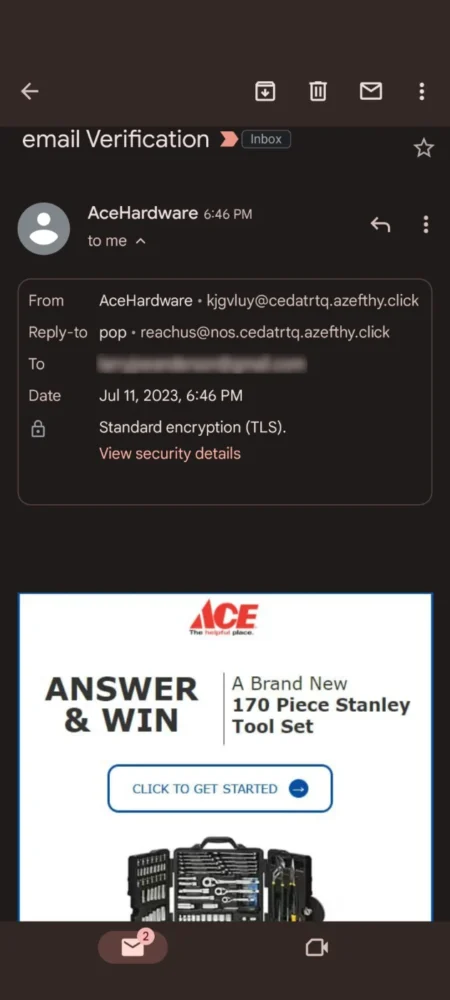
Mismatched Email Addresses
Check the sender’s email address carefully. Scammers often use email addresses that look similar to the legitimate company but have slight variations. Many times they don’t even attempt to hide their email address. They assume people won’t be checking.
This is why I am attempting to educate you on how to check. See these examples below of emails I recently received.
Protecting Yourself from Fake Emails
1. Verify the Source:
Always double-check the sender’s email address to ensure it matches the official one used by the company. If in doubt, and it’s a company that you use, contact the company directly using a verified phone number or website if you need to.
In Gmail:
Android or iPhone – tap on the sender.
On the web – click on the drop down arrow below the sender.
In Apple Mail:
iOS – This requires a few steps. Tap on the email to display the message, then tap on Details. Finally, tap on the sender’s displayed name.
macOS – Click on the displayed name of the email.
Other email clients will be similar. If you don’t know how, email me at larry@thetechboomer.com and I will research it for you.
2. Don’t Click on Suspicious Links:
Avoid clicking on any links or downloading attachments from unknown or suspicious emails. Instead, type the website address directly into your browser to access it securely.
Actually, if you’re not 100% sure that the email is legit, don’t click on a link.
3. Stay Informed:
Keep yourself updated about the latest scams and tactics used by scammers. Being aware of their techniques can help you recognize potential threats.
The Tech Boomer is a great place to keep informed. Enter your email below to receive notices when a new article is published.
4. Use Two-Factor Authentication:
Enable two-factor authentication (2FA) whenever possible. This adds an extra layer of security and makes it harder for scammers to access your accounts.
This article explains what 2FA is, and how to use it.
5. Report Scams:
If you receive a scam email, mark the email as spam. This will notify your email provider and can help protect others from falling victim to the same scheme.
Here are some places you can legitimately report fake emails.
reportphishing@antiphishing.org
You can also report the fake email to the FTC at ReportFraud.ftc.gov.
Conclusion
Scammers are using increasingly sophisticated methods to pose as legitimate companies using fake emails. By familiarizing yourself with common red flags and adopting protective measures, you can significantly reduce your risk of falling for these scams. Remember, the safety of your personal information is your responsibility, and staying vigilant is the key to keeping scammers at bay.
Follow The Tech Boomer to stay safe and informed to enjoy a worry-free digital experience.
And as always, if you have any questions, you can leave a comment below or email me at larry@thetechboomer.com

OTC Hearing Aids for Seniors
OTC Hearing Aids for Seniors, Hearing Aid Amplifiers Devices Rechargeable with Noise Cancelling, Superior Sound Quality for Adults Women Men Hearing Loss, Auto On/Off
View on Amazon →This post may contain affiliate links. As an Amazon Associate, I earn from qualifying purchases.




